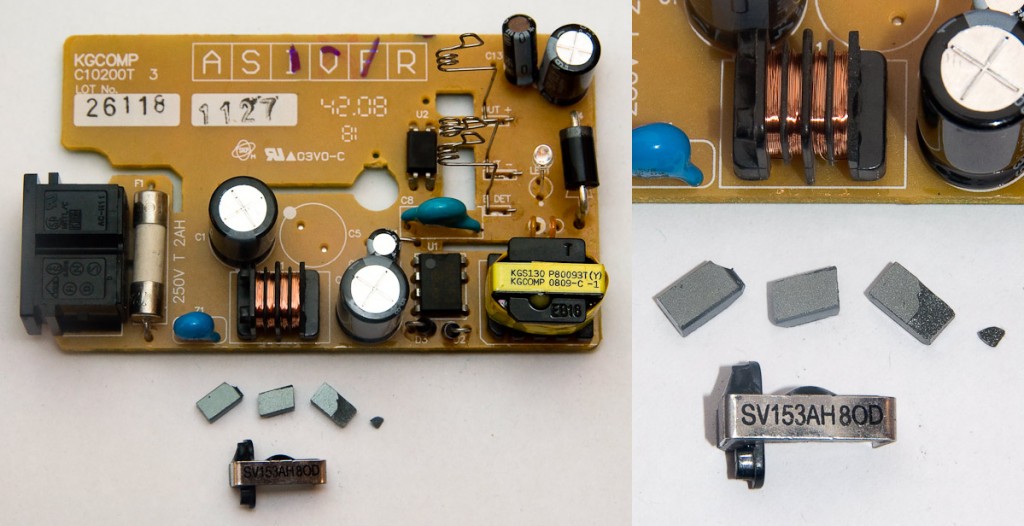
During my holiday in Thailand, I was silly enough to drop my Nikon MH-18a battery charger on the floor from a height of a metre or so. As soon as I picked it up, I heard a rattle. When I looked inside, this is what I found:
The core of the inductor had broken into several pieces. The pieces are shown here, below the copper coils of the inductor. Even though inductor cores are made from ferrite, a notoriously brittle ceramic, I was pretty disappointed to see that the charger was so fragile. After failing to find any suitable replacement parts, I decided to figure out what it was for.
What is the inductor’s job? (Don’t care? Skip to ‘How to fix to fix the problem.’)
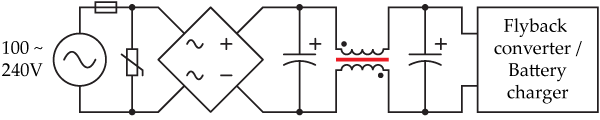
A reverse-engineered schematic of the mains electricity conditioning part of the circuit is shown below, with the broken inductor core depicted in red:
The flyback converter draws pulses of current at a frequency much higher than the 50 or 60 Hz of mains electricity. The two capacitors and inductor combine to form an LC filter, which prevents this high-frequency energy from leaking back into the electricity supply and interfering with other devices.
What effect does the broken core have?
If you plug in the charger while ferrite fragments are still sitting in the box, all sorts of nasty short-circuits could happen.
Even with the inductor effectively absent, the voltage in the two capacitors is still topped up 100 times per second by the mains electricity supply. The flyback converter should therefore have plenty of energy to run the rest of the circuit with, and the battery charger should still function normally. As mentioned in the previous section, the only issue I can identify is that the current waveform being drawn from the electricity supply will be different and noisier, which may cause interference to other devices nearby, or a slight reduction in efficiency.
How to fix the problem
Do not open the charger while it is plugged in, or if it has been plugged in for the past few hours. Capacitors inside the device are charged to potentially lethal voltages during operation, and may maintain this charge after being unplugged. Do not plug the device in unless it has been completely re-assembled, and test it under close observation at first as overheating/fire are possible with any mains electricity device. Do not open the charger if you don’t completely understand all the points mentioned in this box.
Opening up the charger and removing the shattered pieces should remove loose bits of shrapnel that might have caused short circuits, and leave your charger completely functional — the inductor core is completely unnecessary.
To disassemble the charger, simply remove the sticker on the bottom (which is hiding one of the screws) and undo the two screws. The screws are designed to take a funny 6-point star driver, but fortunately a plain small flathead screwdriver did the trick for me.
How to prevent the core from breaking
If you’re very clumsy, or want to cover all your bases, you may wish to open up your charger and preemptively pot (surround) the inductor with epoxy (e.g. Araldite) or similar. Make sure you pay attention to all the notes in the yellow box above, though.